Onion Services
Published:
In the summer 2017 edition of 2600 magazine there is a brilliant article on running onion services as part of a series on censorship resistant services. Onion services provide privacy and security for readers above that which is possible through the use of HTTPS.
Since moving my website to Netlify, my onion service died as Netlify doesn’t provide automatic onion services (although they do offer automated Let’s Encrypt certificate provisioning). If anyone from Netlify is reading this, please consider adding a one-click onion service button next to the Let’s Encrypt button.
For now though, I have my onion service hosted elsewhere. I’ve got a regular onion service (version 2) and also now a next generation onion service (version 3). My setup works like this:
- A cronjob polls my website’s git repository that contains a Hugo static site
- Two versions of the site are built with different base URLs set in the Hugo configuration, one for the regular onion service domain and one for the next generation onion service domain
- Apache is configured for two virtual hosts, one for each domain name
torfrom the Debian archives is configured for the regular onion servicetorfrom git (to have next generation onion service support) is configured for the next generation onion service
The main piece of advice I have for anyone that would like to have an onion service version of their static website is to make sure that your static site generator is handling URLs for you and that your sources have relative URLs as far as possible. Hugo is great at this and most themes should be using the baseURL configuration parameter where appropriate.
There may be some room for improvement here in the polling process, perhaps this could be triggered by a webhook instead.
I’m not using HTTPS on these services as the HTTPS private key for the domain isn’t even controlled by me, it’s controlled by Netlify, so wouldn’t really be a great method of authentication and Tor already provides strong encryption and its own authentication through the URL of the onion service.
Of course, this means you need a secure way to get the URL, so here’s a PGP signed couple of URLs:
-----BEGIN PGP SIGNED MESSAGE-----
Hash: SHA512
As of 2017-09-23, the website at iain.learmonth.me is mirrored by me at
the following onion addresses:
w6d6vblb6vhuqxt6.onion
tvin5bvfwew3ldttg5t6ynlif4t53y3mbmb7sgbyud7h5q6gblrpsnyd.onion
This declaration was written and signed for publication in my blog.
-----BEGIN PGP SIGNATURE-----
iQEzBAEBCgAdFiEEfGEElJRPyB2mSFaW0hedW4oe0BEFAlnG1FMACgkQ0hedW4oe
0BGtTwgAp9PK6x1X9lnPLaeOOEALxn2BkDK5Q6PBt7OfnTh+f53oRrrxf0fmfNMH
Qz/IDY+tULX3TZYbjDsuu+aDpk6YIdOnOzFpIYW9Qhm6jAsX4RDfn1cZoHg1IeM7
bCvrYHA5u753U3Mm+CsLbGihpYZE/FBdc/nE5S6LxYH83QZWLIW19EPeiBpBp3Hu
VB6hUrDz3XU23dXn2U5/7faK7GKbC6TrBG/Z6dUtaXB62xgDIrPEMorwfsAZnWv4
3mAEsYJv9rnIyLbWamXDas8fJG04DOT+2C1NYmZ5CNJ4C7PKZuIYkaoVAp+pzLGJ
6BEBYaRvYIjd5g8xdVC3kmje6IM9cg==
=lUvh
-----END PGP SIGNATURE-----
Note: For the next generation onion service, I do currently have some logging
enabled in the tor daemon as I’m running this service as an experiment to
uncover any bugs that appear. There is no logging beyond the default for the
version 2 hidden service’s tor daemon.
Another note: Current stable releases of Tor Browser do not support next generation onion services, you’ll have to grab an experimental build to try them out.
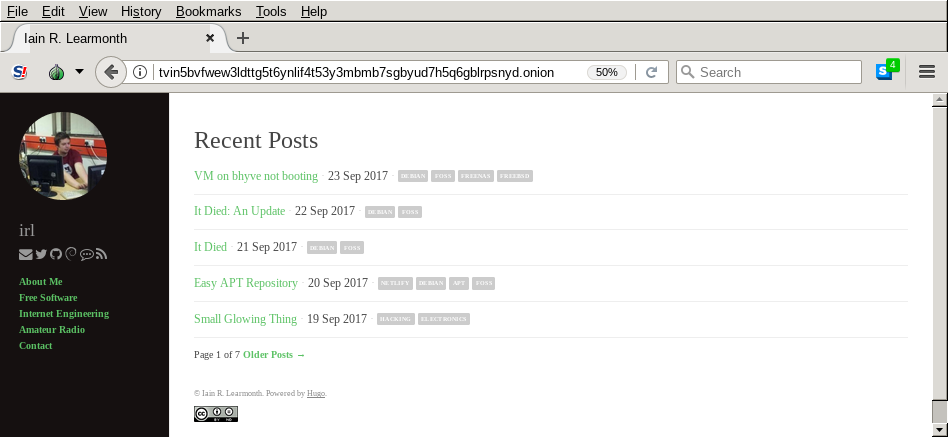
Viewing my next generation onion service in Tor Browser